As the end of the financial year looms many of us are looking at budgets and earmarking areas in our businesses that require spending in the next tax year. IT is one function that I know can cause some sleepless nights for CFOs looking to balance spending with positive ROI.
IT security is one area that doesn’t appear to offer any real return on investment. It’s just something you need to have in place to protect your business from cyber attacks, prevent data breaches and ensure business continuity.
However it can be a key differentiator in the marketplace if you can demonstrate best practice by getting certified, for example through Cyber Essentials.
That said, I know how frustrating it can be for clients when another cyber threat hits the headlines and they have to review their IT budgets once again to see how they can reduce their risk and protect their business.
IT Security Threats
While you can barricade your business against cyber threats with firewalls, anti-virus, email filtering, anti-spam, encryption, UTM etc., there is one major threat to your business that is often overlooked by senior managers. In fact, sometimes they are guilty themselves of lowering cyber security defences as this threat comes from within: your staff.
I’m not talking about disgruntled employees deliberately attacking your systems or allowing access to those with criminal intent, nor am I thinking about absentminded staff leaving sensitive data in full view on a crowded train – although these are also security risks that must be addressed. Instead, I’m focusing on a sophisticated threat that can dupe even senior members of staff: ‘spear phishing’ or ‘whaling’.
Spear phishing has been associated with some of the worse cyber attacks in recent years – eBay, Target, TalkTalk, Sony, to name but a few. In a recent survey conducted by Vanson Bourne and sponsored by Cloudmark, 84% of respondents said that a spear phishing attack had penetrated their organisation’s security defenses. Respondents also said that approximately 28% of spear phishing attacks are getting through their security defenses.
Before delving into what this kind of attack looks like, the good news is that it’s one area of IT security that you can address without spending large sums of money. Raising awareness, robust IT security policies and staff training are your best line of defence when it comes to phishing scams, which will be reassuring if you were wondering how to stretch next year’s IT budget.
What Is Spear Phishing?
Phishing is a technique where scammers send emails to individuals with attachments that contain malicious code, or a link to an infected site, request login details fraudulently or, as is becoming increasingly common, request bank transfers to fraudulent accounts. Most people are aware of this type of scam and are well versed in deleting suspicious looking emails both at home and at work. Often these will use poor grammar and come from unknown senders, who hope that a proportion of emails sent will land in the inboxes of a soft target. However, they become harder to spot when the scammer has more information about the target. For example, some victims of the TalkTalk data breach were targeted in this way even before the data breach hit the news headlines, with emails and telephone calls from individuals who seemed to be legitimate employees of TalkTalk.
This more targeted approach is the difference between phishing and spear phishing, and when used in the business environment scammers will single out individuals who fit certain criteria.
Instead of an email from an unknown sender, your employees could receive an email from someone purporting to work for your organisation. The email itself may look legitimate with company logos and contact information. Your employee may already have had correspondence with this individual, and feel that they’re a trusted source. Then once that trust has been established they hit the recipient with malware and your employee happily opens that attached document or clicks on the link…
Spear phishing uses social engineering principals and is highly targeted. Instead of casting the net wide and hoping that they catch a few fish, the scammers go after a big fish who will deliver exactly what they want. Employees are first identified as likely channels and then nurtured over a period of time with several emails or messages.
Online forums provide an ideal place for scammers to identify targets. Here they can monitor support requests, find individual’s contact details and then email them offering a solution to whatever problem they have. They may start the process in the actual forum, commenting on your employee’s request and suggesting solutions, all the time building trust. This leads on to email communications with the scammer and a spear phishing attack.
Defending Your Business from Spear Phishing
As stated before, protecting your business from spear phishing will not require your entire IT budget. Instead you can reduce the risk of phishing attacks by helping your employees protect your business.
This can be done in two ways:
- Raising awareness of security risks through training & awareness campaigns
- Providing the tools to detect these attacks.
If spear phishing is a new phrase for you, then it’s likely that many of your employees won’t have heard of it either. It’s therefore important to educate them about these kinds of security risks and the consequences of a phishing attack of this type. As these attacks are constantly evolving and becoming more sophisticated, especially those using social engineering, it is worthwhile asking an IT security professional or your IT service provider to deliver this training.
McAfee have a useful quiz that staff can take to see what a phishing attack could look like: Put your phishing knowledge to the test here.
With a more knowledgeable workforce it becomes easier for them to adhere to security guidelines and use techniques that protect your business systems. In brief these include:
- Protecting passwords and logins: employees should never send logins via email, should not click on URLs shared in emails (instead enter them manually or search for websites online), should look for inconsistencies in emails headers, suspicious email addresses and odd looking URLs, and should verify website and email addresses independently,
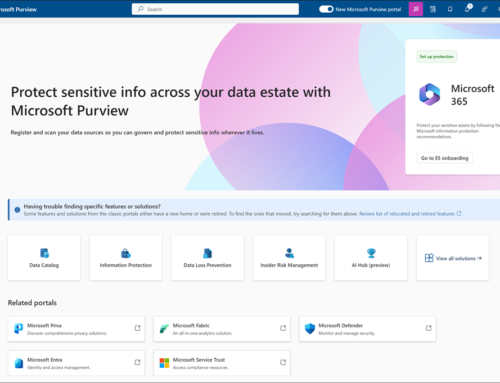
- Protecting against malware: employees should never open or download unsolicited attachments without first double-checking their authenticity, and employers should have clear procedures on how documents are shared within the organisation – for example by using a file sharing system.
- Proper authorisation procedure: ensure that any online banking systems have authorisation procedures in place to ensure a single person, not matter how senior, cannot make a bank transfer without a second person verifying.
Diverting some of next year’s IT security budget into staff training and awareness campaigns could be money well spent, protecting your business long term from phishing attacks.
If you would like to discuss any of the contents above please get in touch, call 0330 124 3599 or email sales@prodriveit.co.uk