We explain why using multifactor authentication alone may not stop a cyber attack – it’s still a vital tool to use but there are other cybersecurity measures you should consider too …
Over the last few years, cyber security advisors – including Pro Drive – have been insisting businesses and individuals use multifactor authentication as an essential tool to prevent devastating and costly cyber attacks on their IT systems and apps.
None of this has changed and, if you are still not following this advice, you are only a few steps away from an almost guaranteed cyber breach.
However, ‘just’ using multifactor authentication is no longer enough. As with any defence to keep out criminals, it is only a matter of time before the bad guys find a way around it and you need to tighten up your security further. Cyber thieves are adopting a number of ways to by-pass multifactor authentication and there have been some recent high-profile breaches demonstrating their success.
Here are some of the common approaches cyber criminals are using to get past multifactor authentication and what can be done to prevent it
Intercepting text messages or phone calls
 One of the original methods used for multifactor authentication, which is still commonly in use, is to have a code sent by text or a telephone call. Unfortunately this is now the most insecure option and criminals have found many ways to circumvent it.
One of the original methods used for multifactor authentication, which is still commonly in use, is to have a code sent by text or a telephone call. Unfortunately this is now the most insecure option and criminals have found many ways to circumvent it.
Tactics specifically targeted at multifactor authentication by text message include transferring the victim’s mobile number to another plan, accessing text through a compromised mobile operator’s portal, deploying malware to mobiles to intercept the message and sim hijacking, where the victim’s SIM is cloned or hijacked.
By moving to a smartphone app for your multifactor authentication you can prevent all of these vulnerabilities. But as we will see later, this still has its shortcomings.
Malicious add-ins
One of the great benefits of cloud applications is their ability to easily integrate with other applications without the need to involve any IT people. To do this, they use a protocol called ‘Oauth’. However this ease of integration can be exploited by cyber criminals, allowing them to create ‘fake applications’ that ‘integrate’ with your cloud applications with the intention of compromising your account.
This is a particular problem with Microsoft 365 and we have written about it in a previous article on our blog.
To help prevent this attack on Microsoft 365, it is possible to set it up so that ‘admin consent grants’ to give access to external applications. They have to be approved centrally via an administrator with sufficient knowledge and time to confirm the request is genuine. Pro Drive do this by default for our managed clients.
Multifactor authentication fatigue
 I would imagine a number of people reading this article will already have what they consider to be multifactor authentication fatigue! However, we are actually referring here to a specific attack method which is also known as ‘MFA bombing’ or ‘brute force’. People using a smartphone app for multifactor authentication with ‘tap to approve’ are vulnerable to this type of attack.
I would imagine a number of people reading this article will already have what they consider to be multifactor authentication fatigue! However, we are actually referring here to a specific attack method which is also known as ‘MFA bombing’ or ‘brute force’. People using a smartphone app for multifactor authentication with ‘tap to approve’ are vulnerable to this type of attack.
The scenario occurs when an attacker has managed to acquire the username and password for an account, usually by a phishing attack or compromised website, then repeatedly attempts to log in with it. They will generate repeated multifactor authentication requests on the user’s smartphone, which research suggests many people will simply ‘accept’ as it’s annoying them and it’s the quickest way to stop it. Of course, they do not realise that in the process they have just let a criminal have free reign on their account.
To help prevent this attack, you should ensure you have an account lock in place after repeatedly failed login attempts. 5 attempts is a good number to keep you secure.
Man in the middle attacks
One of the more recent developments in tactics used to circumvent multifactor authentication systems is the most worrying, as it’s based on a phishing attack. Phishing attacks are still an incredibly successful method used by criminals to trick people into disclosing passwords – made far worse by the fact that a large number of people still believe they will not fall for this trick (these people are the most likely to!).
The attack works by using an email or text message to direct the victim to a ‘fake login’ website – which may for example look identical to a Microsoft 365 login page. Common tactics include sending an email pretending to be from a known contact with a link to a shared document or similar.
The fake login page actually passes on the details to the genuine Microsoft login page and so generates a multifactor authentication request on the victim’s smartphone, or requests entry of the multifactor authentication code. In either case, when the multifactor authentication request is approved, the criminals are into your application.
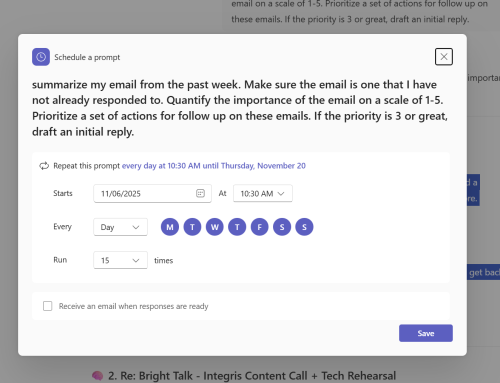
For businesses, technically preventing access to your systems from non-business devices (something that can be done with Microsoft 365) can prevent this. A more ‘belt and braces’ approach is to switch to number-matching authentication – or ‘passwordless’ as it is known by Microsoft. Furthermore, if you can customise your cloud app login page with your logo (something Microsoft allow you to do), it will help reduce the likelihood of staff being tricked.

Other ways multifactor authentication can be bypassed
Even if you have employed all the recommendations mentioned in this article, it does not make you 100% secure. It is still possible for a criminal with access to a compromised computer to get into your web applications by ‘stealing cookies’ – small files that allow you to stay logged in once you have accepted a multifactor authentication request.
Additionally social engineering techniques, where the victim is tricked by a phone call or similar into letting a criminal into their accounts, cannot be prevented by any form of multifactor authentication.
As a result we strongly recommend your computers have robust anti-malware, and you use face or fingerprint recognition to log into them (using something called Windows Hello for Business on Windows PCs) – and that you provide regular cyber security awareness training to your staff. Cyber security awareness training is one of the services we offer.
We are aligning all our clients with these standards. If you are concerned your cyber security might not be up to scratch, please contact us to request a security audit or keep an eye on our events page for details of workshops and webinars where we cover this in more detail.