Although Bring Your own Device (BYoD) seems to have been discussed in enterprise organisations for what seems like years, Pro Drive are finding that the reality is that it is the small to medium (SME) clients that really need to balance the flexibility of enabling access to key information or applications like email with the cost consciousness and apparent simplicity that BYOD enables.
However it is the same SME that typically has the most to lose through loss of business data in a recent IDG report it was concluded that:
“IT organizations are being asked to embrace and support user demands to access essential data, applications and services on tablets and smartphones. And this trend will only accelerate in the coming years. That puts major pressure on IT and security teams to ensure that those devices are used in accordance with policies and best practices designed to safeguard corporate assets.
IT leaders have discovered that there’s a very fine line between giving mobile users the freedom and flexibility to use personal mobile devices, and potential disaster brought on by faulty technology, inappropriate user behaviour, or both. ”
This conclusion is reflected in what Pro Drive are seeing within our own SME client base with requests from our clients to enable access to applications such as email, but securely, and in line with the policies that will ensure these regulated businesses can maintain their business obligations.
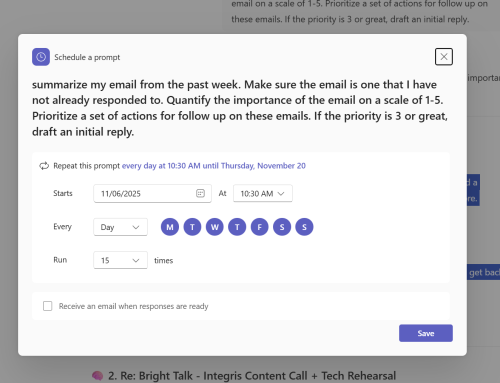
As you have guessed Pro Drive has a mature solution that our clients use that can be applied across many device types and operating systems to manage business email separately from any personal data, allowing authentication and encryption, only approved, and valid users can access sensitive emails and data.
With policies to control the flow of data, restrictions can be implemented restricting sharing by users, forwarding of attachments and copying and pasting. Devices that are lost, stolen or compromised can be selectively wiped to remove the secure email container, all attachments and profiles.